 Access control is a crucial part of any business, as a business owner you need to make sure only the correct people are accessing sensitive information.
Access control is a crucial part of any business, as a business owner you need to make sure only the correct people are accessing sensitive information.
There are three mainÂtypes of access control, each one varies in how it identifies people and what it controls. Learn about each type and how to implement it for enhanced security in your business.
Discretionary Access Control
Discretionary access control (DAC) is one of the most commonly used type of access control. This model allows users to determine their access levels and permissions. It also allows users to transfer their object privileges to others – and even change the security attributes of their objects, systems and information subjects.
DAC is one of the more flexible access control models and can be effective in small organizations with limited IT resources or budgets. However, it can also cause security issues if users are given inappropriate or incorrect access to sensitive data or other resources.
As with any system, it is important to understand the limitations and risks of DAC. Specifically, it is not recommended for businesses or organizations that handle highly confidential data as the level of protection needs to be higher to protect such information.
A more robust access control model is role-based access control (RBAC). This model assigns each user a specific role with specific access permissions. The system administrator then sets up a security policy that controls how the user can access particular areas of a property.
Role-based access control can be particularly useful in commercial properties with many tenants who move in and out of a building at different times of the year. This allows the property manager to quickly and easily grant access permissions to new residents while revoking them for prior tenants.
Additionally, role-based access control is a great way to secure certain areas of the building, such as the pool or gym, that are only accessible during daylight hours. It can also restrict unauthorized access by monitoring a property’s entry and exit points.
A good access control solution will allow you to automate this process by analyzing all of your settings and reporting any changes that impact discretionary access control to you. This will help prevent misconfigurations from allowing intruders to access your network or critical business data.
Role-Based Access Control
Role-based access control is an effective security solution that helps organizations implement strong policies and enables IT administrators to set permissions based on the roles of employees. Unlike discretionary or mandatory access control, this approach helps to ensure that employees only have access to the resources they need to do their jobs.
RBAC is a key component of any security strategy because it can help improve how data and applications are used. It can also reduce the risk of unauthorized users accessing sensitive information or performing unauthorized tasks.
To use RBAC effectively, a business must analyze its workforce and establish roles with the same access needs. This is important because defining roles requires coordination between different departments, and it should be done as early as possible in the planning process. The goal is to create roles that will be easy to update and maintain as the organization grows and changes.
Once the process is complete, regular review and iterative adjustment will be necessary to ensure that the RBAC can support new and existing employees. This will give users the same rights they need to do their work while avoiding bottlenecks and increasing user productivity.
Another benefit of role-based access control is that it allows for greater granularity than rule-based systems. This can enhance security and make it easier for large organizations to scale.
Moreover, role-based systems are more reliable than rules since they can be adjusted without impacting other permissions in the system. This is especially important when adjusting permissions for employees who have recently changed roles within the company or contractors who need temporary access to your network.
Attribute-Based Access Control
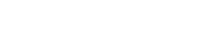
Attribute-Based Access Control (ABAC) is an access control method that uses a combination of attributes to determine user access. It is the next generation of access control technology and has emerged as the preferred solution for data security.
It is a flexible, simple, and secure way to regulate identity-based processes and protect against unauthorized access to sensitive data and systems. It can be used for various access conditions and is an evolution of Role-Based Access Control (RBAC).
ABAC allows organizations to automate identity management tasks and set up policies that allow or deny access based on attributes, rules, and environmental factors. Attribute-based access controls are more granular than role-based controls, which makes them more suitable for large-scale enterprises with complex environments.
Users can access only the resources they need, so there is less chance of errors granting access to users without access. ABAC also makes it easier to manage temporary access and handle job changes, such as when a new employee joins the company or is terminated.
The system also automatically grants or denies access when a user is outside the organization’s time zone and is not logged into the same network as the resource. It can also help ensure compliance with data privacy regulations.
Attribute-based access control is an important tool for securing sensitive corporate data. It has emerged as the next-generation technology to address the shortcomings of Role-Based Access Control solutions and protect against data breaches in the complexities of today’s IT environment.
Identity-Based Access Control
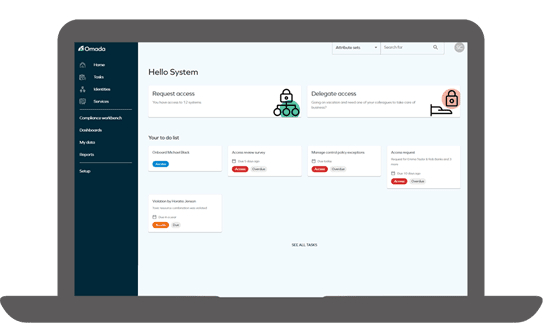
Identity-based access control, also known as identity and access management (IAM), assigns users permissions based on their digital security profile. This allows companies to limit access to sensitive data and prevent lower-level employees from gaining access to important information.
It is often deployed on-premises or in the cloud to ensure that user accounts are properly managed and don’t fall into the hands of malicious actors. It can also ensure that when a user leaves or changes their role, their access rights change accordingly.
Another benefit of this system is that it enables more granular control over users’ access to resources. The system determines whether users can access a resource by comparing their visual or biometric identity with a list of available identities.
In addition to ensuring that users have permission to access the correct resources,ÂIAM systems monitor their activity. They can even catch hackers trying to gain unauthorized access to company networks. This way, companies can keep their data secure and comply with data security regulations like GDPR and the Payment Card Industry Data Security Standard (PCI-DSS).